Network Security Analysis Using Wireshark, Snort, and SO
Video: .mp4 (1280x720, 30 fps(r)) | Audio: aac, 48000 Hz, 2ch | Size: 600 MB
Genre: eLearning Video | Duration: 2.5 hours | Language: English
Learn real technical skills from a real cybersecurity professional with 100% hands-on labs
Video: .mp4 (1280x720, 30 fps(r)) | Audio: aac, 48000 Hz, 2ch | Size: 600 MB
Genre: eLearning Video | Duration: 2.5 hours | Language: English
Learn real technical skills from a real cybersecurity professional with 100% hands-on labs
What you'll learn
How to install and configure Virtualbox
How to install and configure Security Onion on Virtualbox
How to install and configure Kali Linux on Virtualbox
How to install and configure Metasploitable on Virtualbox
How to install and configure Wireshark
How to interpret Snort rules and analyze underlying packet captures
How to use Wireshark and Tcpdump to analyze malicious network traffic
How to use penetration testing / ethical hacking tools (Metasploit, Armitage, Burpsuite, Hydra, Nmap, etc.)
Requirements
Basic TCP/IP Knowledge
Basic information security knowledge
Basic knowledge about packet captures
Basic operating system knowledge (Windows, Linux)
Basics IDS knowledge
PC or Laptop
Virtualbox, Security Onion, Kali Linux, Metasploitable (Free and Open Source Operating Systems)
Description
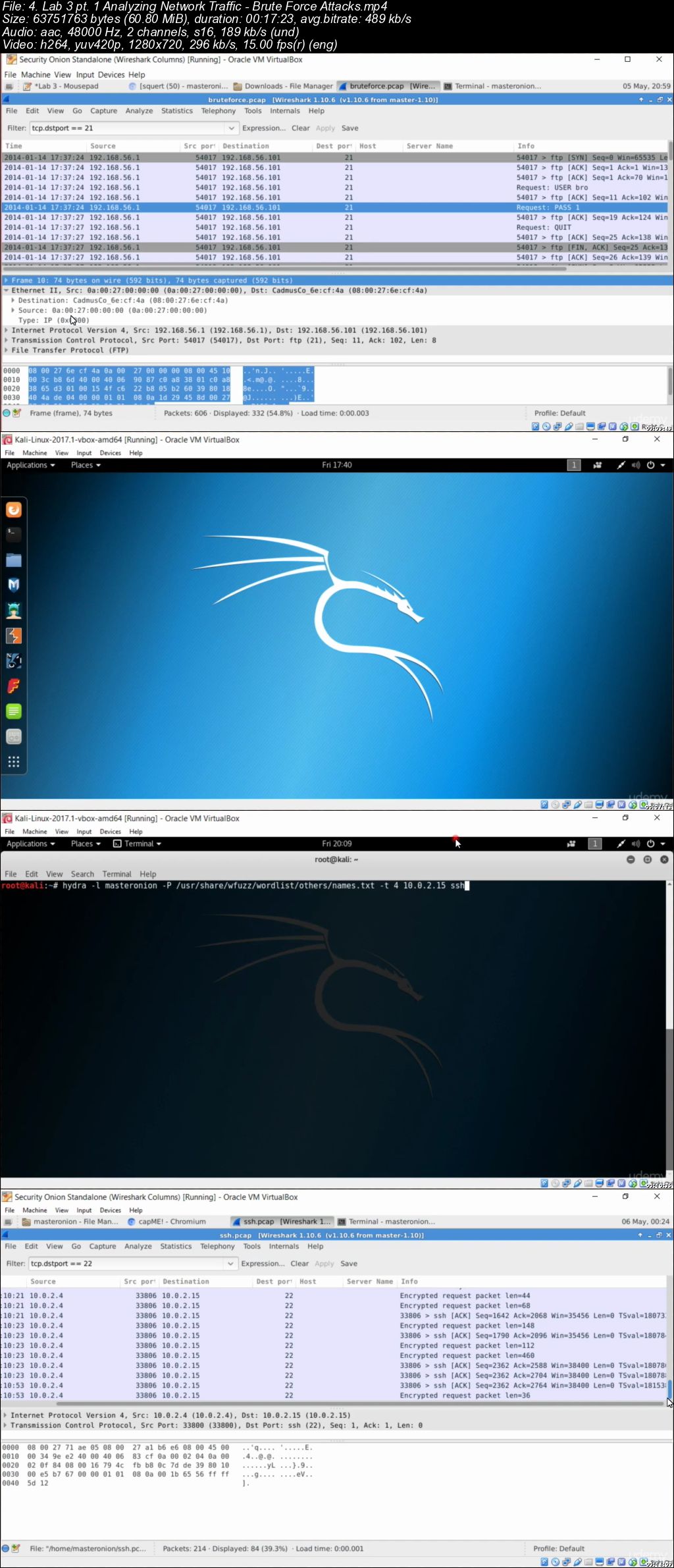
The labs in this course are 100% hands-on and highly technical. Please be prepared to install and configure the necessary software to follow along. This will help you receive the maximum benefit of taking this course. The tools we will be using during this course are Wireshark, Tcpdump, Snort, Burpsuite, Nmap, Tcpreplay, Virtualbox and more. Operating Systems used will be Security Onion, Kali Linux, and Metasploitable. The operating systems and software utilized are all completely free, and can be run on one system using Virtualbox.
We're also going to cover network security analysis with Wireshark and Tcpdump, intrusion detection system analysis with Snort and Squert, and ethical hacking and penetration testing with various tools on Kali Linux. The industry standard tools and methodology utilized in this course will expose you to hands-on skills that are necessary as a network security analyst, and cybersecurity professional in general. The quizzes include written questions, and a mock incident response report based upon findings.
Here's an overview of the labs. Please note that labs 3 and 4 are broken down into two parts due to their length:
Lab 1: Installation/Configuration of Virtualbox and Security Onion
Lab 2: Analyzing Network Traffic - Malware Infection
Lab 3: Analyzing Network Traffic - Brute Force Attacks
Lab 4: Analyzing Network Traffic - Exploitation with Metasploit
Lab 5: Analyzing Network Traffic - Policy Violations
The written quizzes for this class are as follows (attached to Lab 2 and 3 as text documents):
Quiz 1: Lab 2 Questions
Quiz 2: Lab 3 Questions
Who this course is for:
Network Security Analysts
Security Analysts
Cybersecurity Students
Information Systems Security Students
IT Professionals
Cybersecurity Professionals