ISO/IEC 27001 : Information Security Controls Explained
Video: .mp4 (1280x720, 30 fps(r)) | Audio: aac, 48000 Hz, 2ch | Size: 3.05 GB
Genre: eLearning Video | Duration: 32 lectures (7 hour, 4 mins) | Language: English
ISO/IEC 27001 Annex A
Video: .mp4 (1280x720, 30 fps(r)) | Audio: aac, 48000 Hz, 2ch | Size: 3.05 GB
Genre: eLearning Video | Duration: 32 lectures (7 hour, 4 mins) | Language: English
ISO/IEC 27001 Annex A
What you'll learn
Learn about information security controls
Requirements
General knowledge of information security, ISO 27001 Foundation is recommended
Description
This course explains the Information Security Controls of ISO/IEC 27001 Annex A. Annex A of ISO 27001 is probably the most famous annex of all the ISO standards – this is because it provides an essential tool for managing information security risks: a list of security controls (or safeguards) that are to be used to improve the security of information assets.
This course will provide you with an understanding of how Annex A is structured. We will go through all the 114 security controls with easy to understand examples.
Annex A is composed of 14 sections:
A.5 Information security policies – controls on how the policies are written and reviewed
A.6 Organization of information security – controls on how the responsibilities are assigned;
A.7 Human resources security – controls prior to employment, during, and after the employment
A.8 Asset management – controls related to inventory of assets and acceptable use; also for information classification and media handling
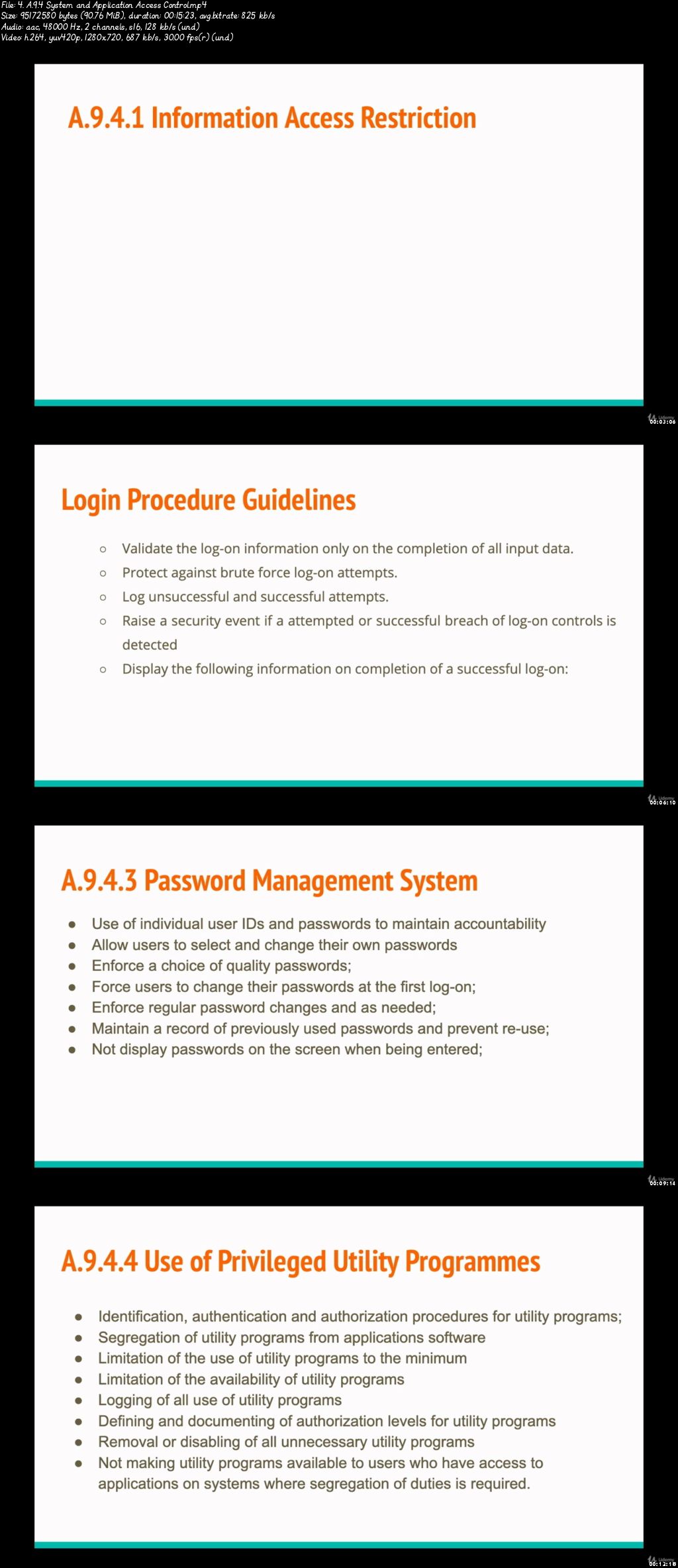
A.9 Access control – controls for the management of access rights of users, systems and applications, and for the management of user responsibilities
A.10 Cryptography – controls related to encryption and key management
A.11 Physical and environmental security – controls defining secure areas, entry controls, protection against threats, equipment security, secure disposal, Clear Desk and Clear Screen Policy, etc.
A.12 Operational security – lots of controls related to the management of IT production: change management, capacity management, malware, backup, logging, monitoring, installation, vulnerabilities, etc.
A.13 Communications security – controls related to network security, segregation, network services, transfer of information, messaging, etc.
A.14 System acquisition, development and maintenance – controls defining security requirements, and security in development and support processes
A.15 Supplier relationships – controls on what to include in agreements, and how to monitor the suppliers
A.16 Information security incident management – controls for reporting events and weaknesses, defining responsibilities, response procedures, and collection of evidence
A.17 Information security aspects of business continuity management – controls requiring the planning of business continuity, procedures, verification and reviewing, and IT redundancy
A.18 Compliance – controls requiring the identification of applicable laws and regulations, intellectual property protection, personal data protection, and reviews of information security
Who this course is for:
IT employees who want to implement information security controls in their entreprise