Full Ethical Hacking & Penetration Testing Course
Video: .mp4 (1280x720, 30 fps(r)) | Audio: aac, 44100 Hz, 2ch | Size: 14.6 GB
Genre: eLearning Video | Duration: 369 lectures (30 hour, 13 mins) | Language: English
Video: .mp4 (1280x720, 30 fps(r)) | Audio: aac, 44100 Hz, 2ch | Size: 14.6 GB
Genre: eLearning Video | Duration: 369 lectures (30 hour, 13 mins) | Language: English
Ethical Hackers are in demand.Learn Web Application Penetration testing, Wi-Fi Hacking, Web Hacking, Metasploit & more!
What you'll learn
Full Ethical Hacking & Penetration Testing Course
Advanced Web Application Penetration Testing
Terms, standards, services, protocols and technologies
Setting up Virtual Lab Environment
Modern Web Applications
Web Application Hosting
Discovering Web applications on the Same Server
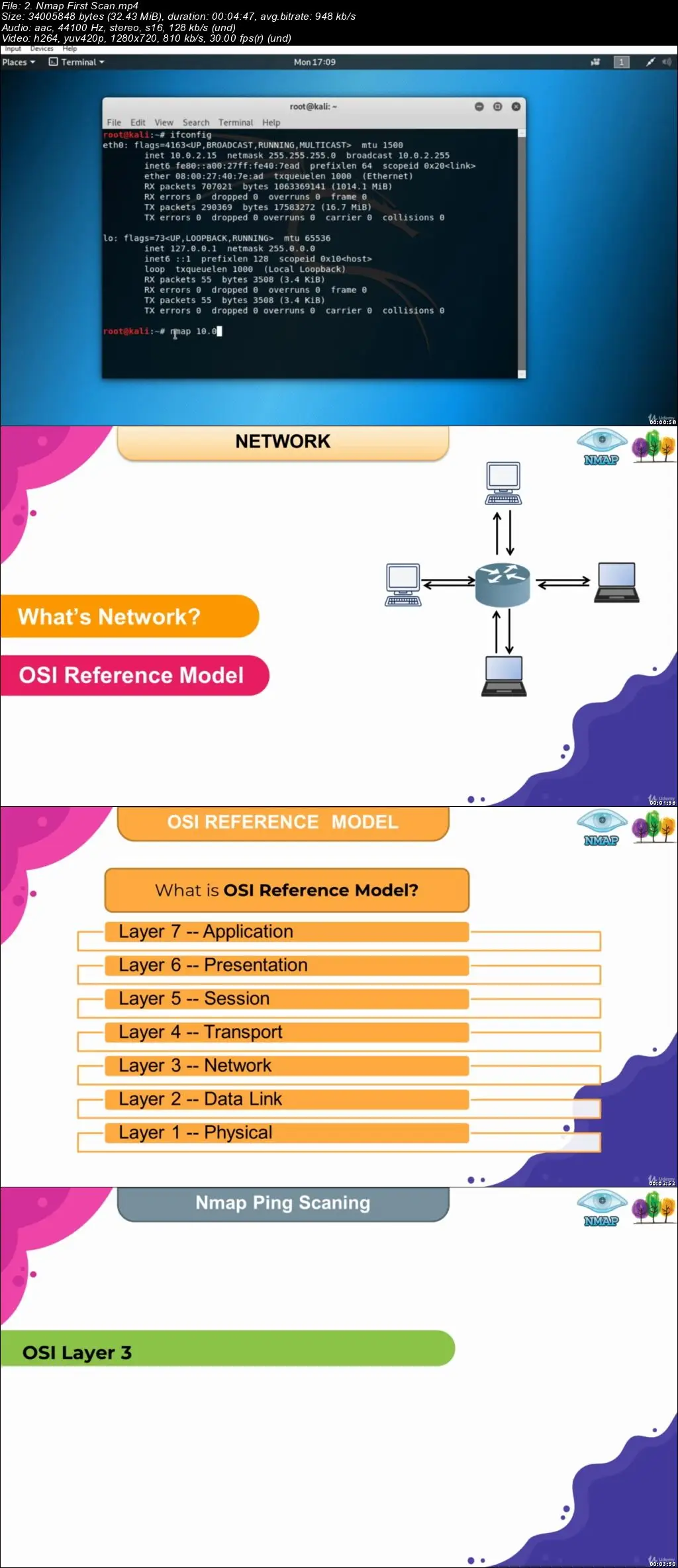
Learn Nmap Basic and Advanced Scanning Techniques
Learn about network scan types
With Nmap, you will learn to identify the operating system and running service versions of the target system
You will learn options for bypassing firewall, IPS & IDS systems with Nmap
How to scan without getting caught in IPS & IDS systems
What is Port ? What is TCP/UDP port ?
How to scan TCP or UDP services?
Importance of Penetration Testing
Types of Penetration Testing
Metasploit Filesystem and Libraries
Nmap Integration and Port Scanning
SMB and Samba Enumeration
Exploitation and Gaining Access
Post-exploitation-Meterpreter
Meterpreter Python/Powershell Extension
Antivirus Evasion and Cleaning
The very latest up-to-date information and methods
During the course you will learn both the theory and how to step by step setup each method
Learn how to create undetectable malware using MSFvenom, Veil, TheFatRat, Empire Project, etc
Learn embedding malware in pdf and doc files
Learn the working mechanism of Social Engineering Toolkit
Learn social engineering techniques and terminologies
Learn how to collect information about people by using OSINT (Open Source Intelligence)
Learn how to use FOCA, Web Archieve, The Harvester & Recon-NG
Wireshark: Sniffing the Network Traffic
Hping for Active Scan and DDoS Attacks
Ping Scan to Enumerate Network Hosts
Exploitation Tool: Metasploit Framework (MSF)
Information Gathering Over the Internet Tools
Wi-Fi Adapter Settings
Wi-Fi Network Fundamentals,IEEE 802.11
Wireless Operating Modes : Ad-hoc, Infrastructure, Monitor modes.
Wi-Fi Network Interaction, Authentication Methods
Requirements
Minimum 8 GB RAM
100 GB Free Harddisk space
64-bit processor
Wi-Fi Adapter(for Wi-Fi Hacking Sections)
Microsoft Windows 7, 8, 10 or Apple Mac OS X 10.12 and later versions
Enable virtualization technology on BIOS settings, such as “Intel-VTx”
A strong desire to understand hacker tools and techniques
Be able to download and install all the free software and tools needed to practice
A strong work ethic, willingness to learn and plenty of excitement about the back door of the digital world
Nothing else! It’s just you, your computer and your ambition to get started today
Description
Welcome to the "Full Ethical Hacking & Penetration Testing Course" course.
68% of business leaders say cybersecurity risks are increasing. As threats rise, companies are trying hard to attract and retain more IT security talent.
But filling IT security roles is proving difficult. Many businesses are facing serious recruitment challenges. There are not enough qualified candidates to fill the roles needed.
The industry faces a skills gap which looks set to increase as cyber threats rise. It is predicted that there will be 3.5 million unfilled cybersecurity roles by 2021. If you are considering a career move, the skills gap represents an excellent opportunity. This course is a great start for you.
This course starts at beginner levels so you don’t need to have previous knowledge of Ethical Hacking. In this course, we will also cover the topic of Wi-Fi Hacking because Wi-Fi hacking is easier than hacking a device connected to that WiFi. There are many free tools that can hack the less secure Wi-Fi router. Apart from this, there are also advanced tools that work on backtrack and can even hack Wi-Fi router with high security.
We are going to start by figuring out what the security issues are that are currently in the field and learn testing methodologies and types. Then we are going to build a lab environment for you to apply what you get from the course and of course, the lab is gone cost you nothing. Then we are going to start with some theory, you know, you should have the philosophy so we can always stay on the same page.
Basic web and internet technologies such as HTML, HTTP, Document Object Model, and so on, these are absolutely needed so that we can complete the testing experience. And then we are gonna cover the reconnaissance section, we will gather information about the target and how to use that information to model an attack. After that, we will tackle the user management issues. Apart from that, we will also try to expose the session management problems.
In the input validation section, we are gonna show why data validation is absolutely important for web applications. So attacks such as Cross-Site Scripting, SQL Injection, and many more we are gonna examine the whole bunch of different types. We also have a cryptography section with some basic attacks. After that, we will discuss some known web application attacks (such as Drupal SQL injection aka Druppageddon).
In this course I tried to show the importance of using free tools and platforms, so you don’t need to buy any tool or application.
By registering the course you will have lifetime access all resources, practice videos, and will be able to ask questions about related topics whenever you want.
A step by step approach will help you to track your progress on the go and learn needed skills gradually at your own pace. At the end of this course, you will both have the knowledge and a practical skillset about using network scanning, finding vulnerabilities on systems, and learning the general competencies of ethical hackers.
Here’s just some of what you’ll learn by the end of the course,
Understand the main terminology of Network Scanning and Finding Vulnerabilities in devices in a network
Using Nmap with full knowledge and experience
How to scan a network for scripts
Learn about network scan types
Learn how to use Hping
Wireless Operating Modes: Ad-hoc, Infrastructure, Monitor modes.
Wireless Packet Types
Analysing Packet Types with Wireshark
Wi-Fi Network Interaction, Authentication MethodsWEP vs WPA/WPA2
What is the TCP/IP model and how does it work
What is OSI model? How does it work
What is Port? What is the TCP/UDP port
How to scan TCP or UDP services
How active services are detected
How to scan without getting caught in IPS & IDS systems
How to interpret Nmap outputs
Nmap scripting (NSE) and more
WPA/WPA2 Cracking using GPUs with Hashcat
Key Reinstallation Attacks (KRACK)
WPS PIN Attacks and more…
How open source intelligence (OSINT) can be gathered and used for hacking into systems
How to send fake emails
Learn about vishing (Voice Phishing) tools and techniques
How to use Empire Project, MSFvenom, Veil, and TheFatRat
Testing Methodologies and Types,
Basic Web and Internet Technologies such as HTML, HTTP, Document Object Model and so on,
To Gather Information About the Target and Use This Information to Model an Attack.
User Management Issues.
Exposing The Session Management Problems.
Data Validation
Wardriving with Kismet, Mapping with Google Earth
Rogue Access Points with Airbase-ng, Wifi Pumpkin 3, Fluxion
Handshake Snooper and Captive Portal Attack with Fluxion
Attacks such as Cross-Site Scripting, SQL Injection and many more
Some Basic Attacks in Cryptography
Web Application Attacks Such As Drupal SQL injection ( aka Druppageddon )
And More to Enrich Your Penetration Testing Skills.
And much, much more… We have also added practical lab sessions in our course for sharping up your skills.
Fresh content
It’s no secret how technology is advancing at a rapid rate. New tools are released every day, and it’s crucial to stay on top of the latest knowledge for being a better security specialist.
Video and Audio Production Quality
All our videos are created/produced as high-quality video and audio to provide you the best learning experience.
You will be,
Seeing clearly
Hearing clearly
Moving through the course without distractions
You'll also get:
Lifetime Access to The Course
Fast & Friendly Support in the Q&A section
Udemy Certificate of Completion Ready for Download
Dive in now!
We offer full support, answering any questions.
See you in the course!
IMPORTANT: This course is created for educational purposes and all the information learned should be used when the attacker is authorized.
Who this course is for:
People who are willing to make a career in Cyber Security
Cyber Security Consultants who support / will support organizations for creating a more secure environment
Anyone who want to do a Penetration Testing against Wi-Fi networks.
Anyone who are the System administrators and want to audit their Wi-Fi network configuration.
Anyone who wants to be a White Hat Hacker
Anyone who wants to learn how to crack password hashes
Those who want to start from scratch and move forward
People who want to take their hacking skills to the next level