Ethical Hacking with Hardware Gadgets
Video: .mp4 (1280x720, 30 fps(r)) | Audio: aac, 48000 Hz, 2ch | Size: 111 MB
Genre: eLearning Video | Duration: 1 hour | Language: English
Video: .mp4 (1280x720, 30 fps(r)) | Audio: aac, 48000 Hz, 2ch | Size: 111 MB
Genre: eLearning Video | Duration: 1 hour | Language: English
Learn all about USB attacks, USB Rubber Ducky, HID Attacks, BadUSB, keystroke injections, WiFi jamming.
What you'll learn
Explore the threat landscape: USBs, WiFi jammers
Learn common tools and techniques used
Practical skillset in defeating hardware-based threats
Extend your cyber security know-how for hardware-based tools
Requirements
General IT know-how
possibility of installing new software (Windows, macOS)
Interest in IT-Security and hardware projects
basic programming know-how
Description
In this course we will have a look at a couple of hardware gadgets which can be used for hacking.
USB Hacking
I will present you how a keystroke injection attack works and present USB sticks like USB Rubber Ducky and while show you how to write your own scripts to exploit this vulnerability.
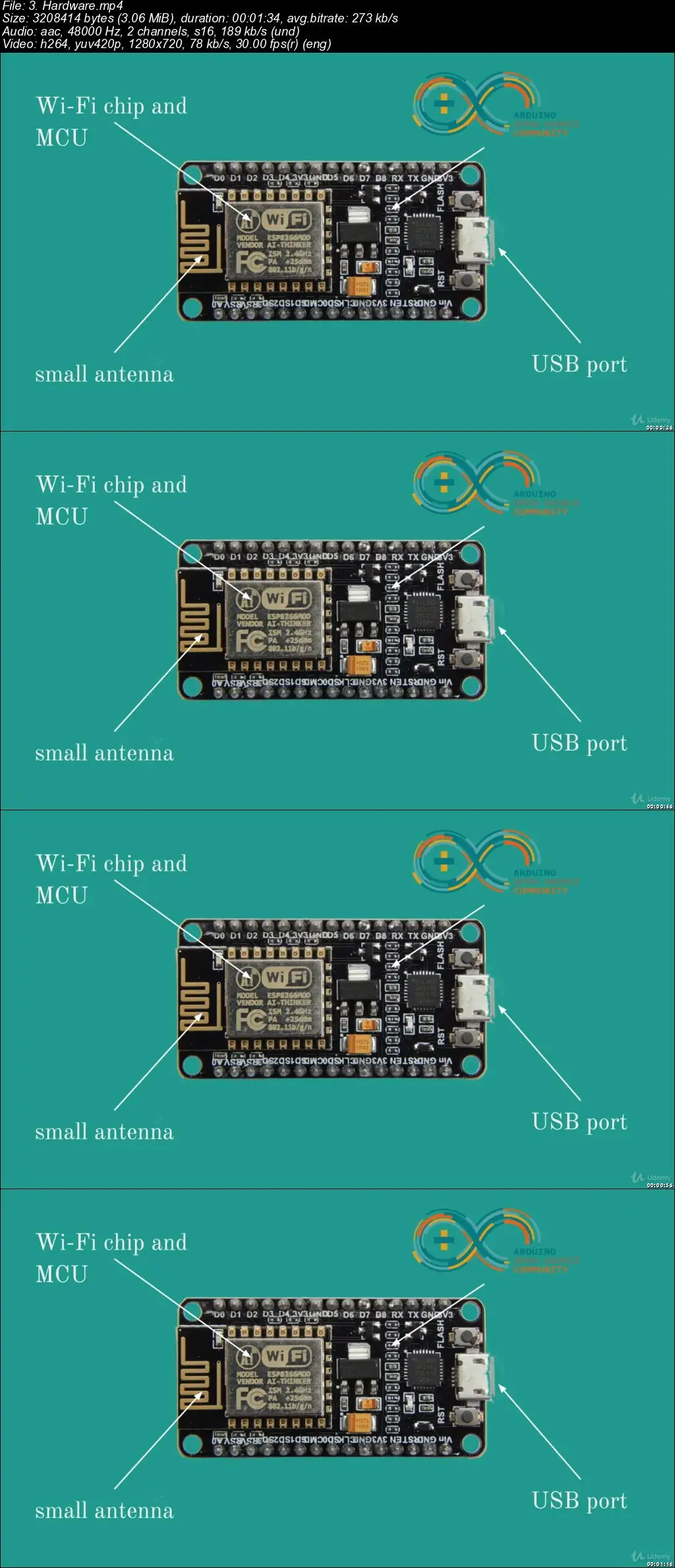
In a series of lecture I will show you how you can build a lower-cost version of the USB Rubber Ducky by using cheap Chinese made development boards which are compatible with the Arduino platform.
After you understand how the attack works and are able to build your own device, I will explain what options are available in order to protect yourself.
WiFi jamming
WiFi Jammers or to call them more properly WiFi deauthers, are basically a very easy way of kicking everybody out from a specific Wi-Fi network and if wanted, making the Wi-Fi network useless.
This section is dealing with a known vulnerability in the IEEE 802.11 (Wi-Fi) protocol even with WPA2. While the data you are transferring by the Wi-Fi network is encrypted and better protected, the problem are the so called management frames that are not always authenticated, thus allowing an attacker for example to disconnect the devices from the network by sending a so-called deauthentication frame, used to terminate a connection.
I will show you how it is done and what you can do to protect yourself.
Expected more?
I plan to explore other devices and attack techniques, based on your feedback!
Who this course is for:
Users interested in IT-security and and privacy
Anyone who wants to extend their know-how in IT-security
Network / IT Administrators