Complete Ethical Hacking and Penetration Testing Course
Video: .mp4 (1280x720, 30 fps(r)) | Audio: aac, 44100 Hz, 2ch | Size: 11.4 GB
Genre: eLearning Video | Duration: 338 lectures (27 hour, 15 mins) | Language: English
Video: .mp4 (1280x720, 30 fps(r)) | Audio: aac, 44100 Hz, 2ch | Size: 11.4 GB
Genre: eLearning Video | Duration: 338 lectures (27 hour, 15 mins) | Language: English
My Ethical Hacking course includes Web Hacking, Phishing, NMAP, Password Cracking, Penetration Testing, Metasploit &more
What you'll learn
Learn Ethical Hacking with Penetration Testing
Setting Up The Laboratory
Install Kali Linux - a penetration testing operating system
Install Windows & vulnerable operating systems as virtual machines for testing
Discover vulnerable applications
What is TCP/IP model
What is OSI model
How to scan TCP or UDP services?
Exploit vulnerabilities to gain control over systems
Vulnerability scanning, Exploit, Post Exploit, Payload
Learn about script scanning
Gain control over computer systems using server side attacks
Gathering password hashes, cracking passwords, taking screenshots, logging keystrokes etc.
Using backdoors to persist on the victim machine
Information Gathering Over the Internet Tools
Web App Hacking Tools
Social Engineering Toolkit (SET) for Phishing
The very latest up-to-date information and methods
What is Port ? What is TCP/UDP port ?
Requirements
8 GB (Gigabytes) of RAM or higher (16 GB recommended)
64-bit system processor is mandatory
20 GB or more disk space
Enable virtualization technology on BIOS settings, such as “Intel-VTx”
Modern Browsers like Google Chrome (latest), Mozilla Firefox (latest), Microsoft Edge (latest)
All items referenced in this course are Free
A computer for installing all the free software and tools needed to practice
A strong desire to understand hacker tools and techniques
Be able to download and install all the free software and tools needed to practice
A strong work ethic, willingness to learn and plenty of excitement about the back door of the digital world
Nothing else! It’s just you, your computer and your ambition to get started today
Description
Welcome to Complete Ethical Hacking and Penetration Testing Course.
My Complete Ethical Hacking and Penetration Testing Course is for everyone! If you don’t have any previous experience on a Ethical Hacking, not a problem!
This course is expertly designed to teach everyone from complete beginners, right through to pro hackers. You'll go from beginner to extremely high-level and I will take you through each step with hands-on examples.
And if you are a pro-Ethical Hacker, then take this course to quickly absorb the latest skills, while refreshing existing ones.
The good news is:
All applications and tools recommended are free. So you don’t need to buy any tool or application.
Before attending the course please read below the course requirements.
This course is focused on the practical side of penetration testing and ethical hacking but I also will share with you the theory side of each attack. Before jumping into Penetration Testing or other practices with Ethical Hacking tools you will first learn how to set up a lab and install needed software on your machine. In this course, you will have a chance to keep yourself up-to-date and equip yourself with a range of Ethical Hacking skills.
When you finish this course you will learn the most effective steps to prevent attacks and detect adversaries with actionable techniques that you can directly apply when you get back to work. I am coming from the field and I will be sharing my 20 years' experience with all of you. So you will also learn tips and tricks from me so that you can win the battle against the wide range of cyber adversaries that want to harm your environment.
Requirements
CPU: 64-bit Intel i5/i7 (4th generation +) - x64 bit 2.0+ GHz processor or more recent processor is mandatory for this class (Important - Please Read: a 64-bit system processor is mandatory)
Virtualization Technology: Enable virtualization technology on BIOS settings, such as “Intel-VTx”.
RAM : 8 GB (Gigabytes) of RAM or higher (16 GB recommended)
Modern Browsers:
Google Chrome (latest)
Mozilla Firefox (latest)
Microsoft Edge (latest)
Disk : 20 GB or more disk space
Here is the list of what you’ll learn by the end of course,
Setting Up The Laboratory
Set Up Kali Linux from VM
Set Up Kali Linux from ISO File
Set Up a Victim: Metasploitable Linux
Set Up a Victim: OWASP Broken Web Applications
Set Up a Victim: Windows System
Penetration Test
Penetration Test Types
Security Audit
Vulnerability Scan
Penetration Test Approaches: Black Box to White Box
Penetration Test Phases: Reconnaissance to Reporting
Legal Issues Testing Standards
Network Scan
Network Scan Types
Passive Scan With Wireshark
Passive Scan with ARP Tables
Active Scan with Hping
Hping for Another Purpose: DDos
Nmap for Active Network Scan
Ping Scan to Enumerate Network Hosts
Port Scan with Nmap
SYN Scan, TCP Scan, UDP Scan
Version & Operating System Detection
Input & Output Management in Nmap
Nmap Scripting Engine
How to Bypass Security Measures in Nmap Scans
Some Other Types of Scans: XMAS, ACK, etc.
Idle (Stealth) Scan
Vulnerability Scan
Introduction to Vulnerability Scan
Introduction to a Vulnerability Scanner: Nessus
Nessus: Download, Install & Setup
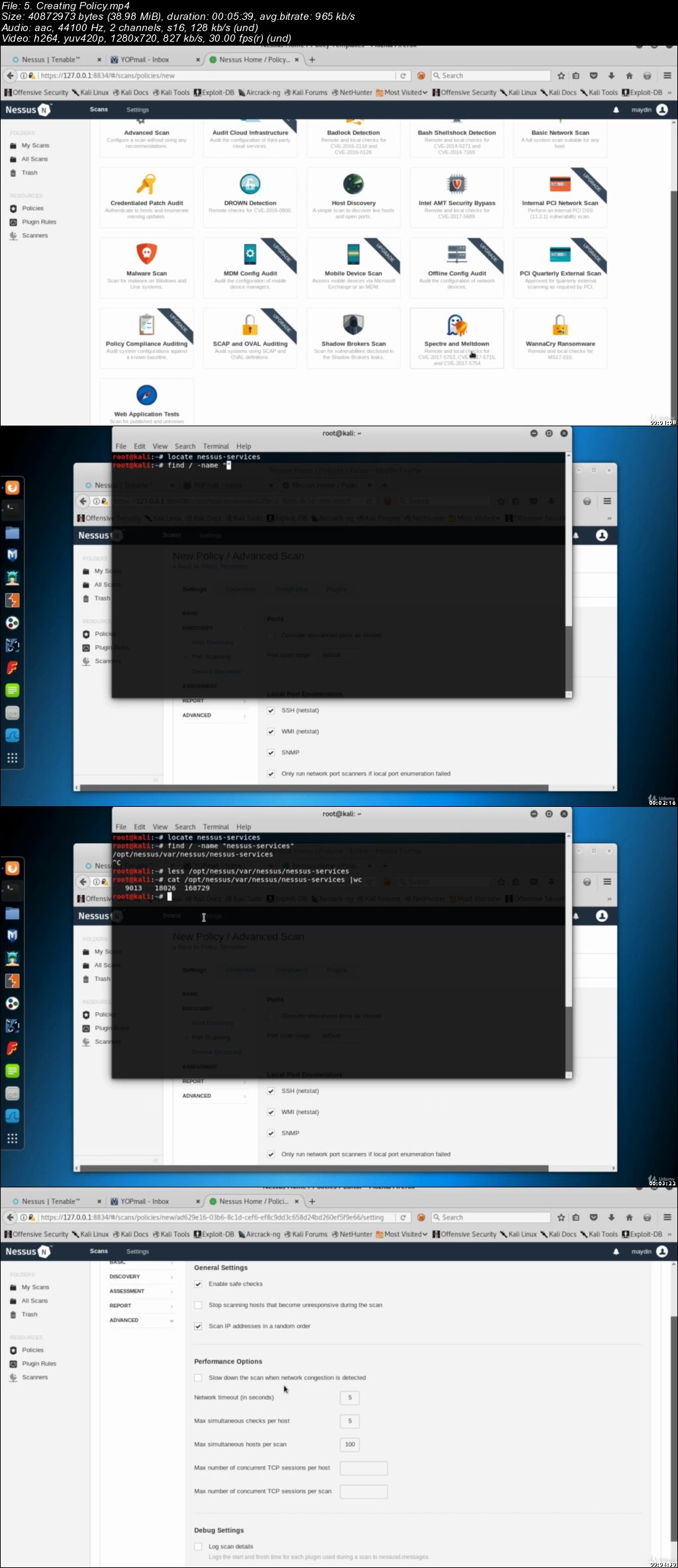
Nessus: Creating a Custom Policy
Nessus: First Scan
An Aggressive Scan
Nessus: Report Function
Exploitation
Exploitation Terminologies
Exploit Databases
Manual Exploitation
Exploitation Frameworks
Metasploit Framework (MSF)
Introduction to MSF Console
MSF Console & How to Run an Exploit
Introduction to Meterpreter
Gaining a Meterpreter Session
Meterpreter Basics
Pass the Hash: Hack Even There is No Vulnerability
Post-Exploitation
Persistence: What is it?
Persistence Module of Meterpreter
Removing a Persistence Backdoor
Next Generation Persistence
Meterpreter for Post-Exploitation with Extensions: Core, Stdapi, Mimikatz…
Post Modules of Metasploit Framework (MSF)
Collecting Sensitive Data in Post-Exploitation Phase
Password Cracking
Password Hashes of Windows Systems
Password Hashes of Linux Systems
Classification of Password Cracking
Password Cracking Tools in Action: Hydra, Cain and Abel, John the Ripper…
OSINT (Open Source Intelligent) & Information Gathering Over the Internet
Introduction to Information Gathering
Using Search Engines to Gather Information
Search Engine Tools: SiteDigger and SearchDiggity
Shodan
Gathering Information About the People
Web Archives
FOCA - Fingerprinting Organisations with Collected Archives
Fingerprinting Tools: The Harvester and Recon-NG
Maltego - Visual Link Analysis Tool
Hacking Web Applications
Terms and Standards
Intercepting HTTP & HTTPS Traffics with Burp Suite
An Automated Tool: Zed Attack Proxy (ZAP) in Details
Information Gathering and Configuration Flaws
Input & Output Manipulation
Cross Site Scripting (XSS)
Reflected XSS, Stored XSS and DOM-Based XSS
BeEF - The Browser Exploitation Framework
SQL Injection
Authentication Flaws
Online Password Cracking
Authorisation Flaws
Path Traversal Attack
Session Management
Session Fixation Attack
Cross-Site Request Forgery (CSRF)
Social Engineering & Phishing Attacks
Social Engineering Terminologies
Creating Malware - Terminologies
MSF Venom
Veil to Create Custom Payloads
TheFatRat - Installation and Creating a Custom Malware
Embedding Malware in PDF Files
Embedding Malware in Word Documents
Embedding Malware in Firefox Add-ons
Empire Project in Action
Exploiting Java Vulnerabilities
Social Engineering Toolkit (SET) for Phishing
Sending Fake Emails for Phishing
Voice Phishing: Vishing
Network Fundamentals
Reference Models: OSI vs. TCP/IP
Demonstration of OSI Layers Using Wireshark
Data Link Layer (Layer 2) Standards & Protocols
Layer 2: Ethernet - Principles, Frames & Headers
Layer 2: ARP - Address Resolution Protocol
Layer 2: VLANs (Virtual Local Area Networks)
Layer 2: WLANs (Wireless Local Area Networks)
Introduction to Network Layer (Layer 3)
Layer 3: IP (Internet Protocol)
Layer 3: IPv4 Addressing System
Layer 3: IPv4 Subnetting
Layer 3: Private Networks
Layer 3: NAT (Network Address Translation)
Layer 3: IPv6
Layer 3: DHCP - How the Mechanism Works
Layer 3: ICMP (Internet Control Message Protocol)
Layer 3: Traceroute
Introduction to Transport Layer (Layer 4)
Layer 4: TCP (Transmission Control Protocol)
Layer 4: UDP (User Datagram Protocol)
Introduction to Application Layer (Layer 5 to 7)
Layer 7: DNS (Domain Name System)
Layer 7: HTTP (Hyper Text Transfer Protocol)
Layer 7: HTTPS
Network Layer & Layer-2 Attacks
Creating Network with GNS3
Network Sniffing: The “Man in the Middle” (MitM)
Network Sniffing: TCPDump
Network Sniffing: Wireshark
Active Network Devices: Router, Switch, Hub
MAC Flood Using Macof
ARP Spoof
ARP Cache Poisoning using Ettercap
DHCP Starvation & DHCP Spoofing
VLAN Hopping: Switch Spoofing, Double Tagging
Reconnaissance on Network Devices
Cracking the Passwords of the Services of Network Devices
Compromising SNMP: Finding Community Names Using NMAP Scripts
Compromising SNMP: Write Access Check Using SNMP-Check Tool
Compromising SNMP: Grabbing SNMP Configuration Using Metasploit
Weaknesses of the Network Devices
Password Creation Methods of Cisco Routers
Identity Management in the Network Devices
ACLs (Access Control Lists) in Cisco Switches & Routers
SNMP (Simple Network Management Protocol) Security
You'll also get:
Lifetime Access to The Course
Fast & Friendly Support in the Q&A section
Udemy Certificate of Completion Ready for Download
Enroll now to become a professional Ethical Hacker!
IMPORTANT: This course is created for educational purposes and all the information learned should be used when the attacker is authorized.
Who this course is for:
People who want to start from scratch and to move more advanced level
Anyone who wants to learn network scan techniques
Leaders of incident handling teams
People who want to take their Hacking skills to the next level
People who are cyber security experts
People who want job transition into Cyber Security
System administrators who are on the front lines defending their systems and responding to attacks
Other security personnel who are first responders when systems come under attack