Web Security: Injection Attacks With Java & Spring Boot
Last updated 8/2024
MP4 | Video: h264, 1280x720 | Audio: AAC, 44.1 KHz
Language: English (US) | Size: 2.81 GB | Duration: 8h 52m
Last updated 8/2024
MP4 | Video: h264, 1280x720 | Audio: AAC, 44.1 KHz
Language: English (US) | Size: 2.81 GB | Duration: 8h 52m
Ethical Hacking, Web Application & Spring Security - Master Injection Attacks with NoSQL, LDAP, LOG, CSV & SQL Injection
What you'll learn
Ethical hacking with injection attacks
Web security
Secure coding
SQL Injection with PostgreSQL
NoSQL Injection with MongoDB
LDAP Injection with OpenLDAP
LOG Injection
CSV Injection
Spring security Form login authentication
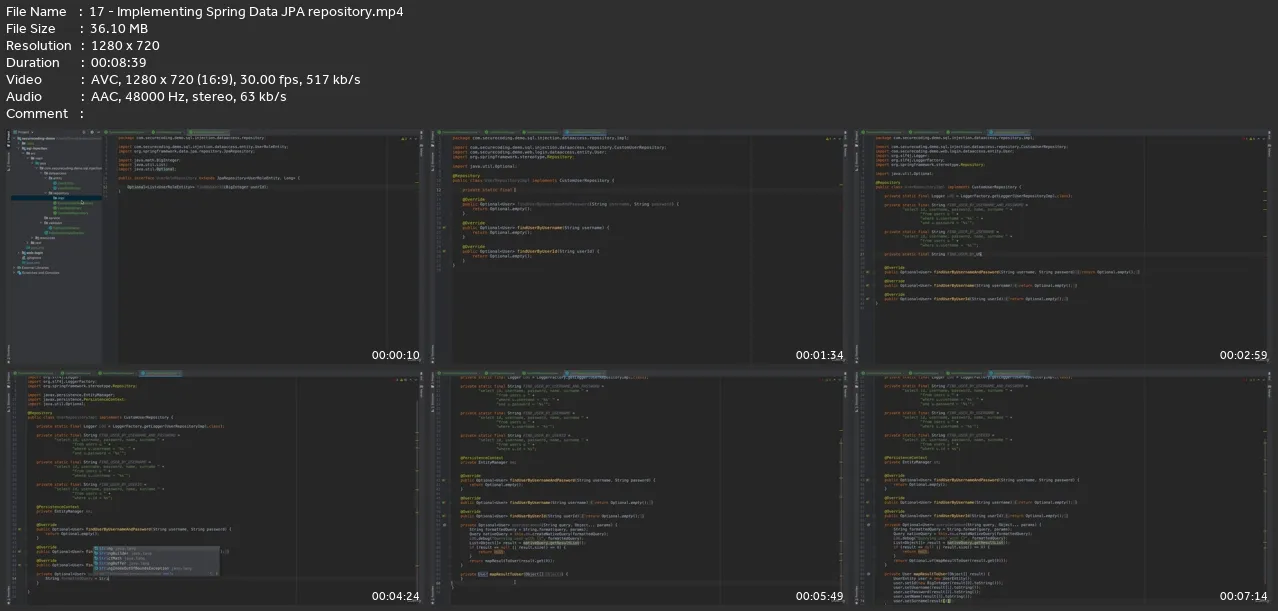
Spring Data JPA
Spring Data MongoDB
Spring LDAP
Spring Validation
Requirements
Knowledge of Java
Basic knowledge of Spring Framework
Basic knowledge of SQL
Basic knowledge of Web application development
Description
Are you a Java web developer and want to write secure code? Do you want to learn Ethical hacking and Web application security? With this hands-on injection attacks course you will start learning web security using one of the top vulnerabilities of OWASP Top 10 list. Injection attack is still listed in top 3 attacks in the OWASP Top 10 and it is important to prevent against injection attacks to develop secure web applications. Krzysztof Telka: "Nice examples, where the host is presenting step by step how to exploit the application and then how to prevent. Lot of nice tools, features to check and examine the web page in case of hackers attack. CSV/Log4J/SQL made big wow effect on my face. The atendeers they will not be dissapointed Great job Ali, Thank you!"You can always use the latest versions for spring boot, and other dependencies in this course. I will be constantly updating the dependency version in the last section's lectures. You may check that to see the required code and configuration changes for updated versions. Also if you would like to use subtitles during the course, you can turn on the captions on videos. I suggest using subtitles to make it easier to follow the lectures. As part of the blue and red security teams,I have a practical knowledge and I am here to help you learn the injection vulnerability in detailIn this course, you will focus on different type of injection attacks;SQL InjectionNoSQL injectionLDAP injectionLOG injectionCSV injectionEthical hacking and Web application security are the two important subjects of Cyber Security field and having practical knowledge about Injections will enable you to better understand the security concepts and make a quick start. In this course you will follow defense-in-depth principle and apply multiple solutions to each vulnerability to secure the web application in multiple layers. You will follow a hands-on approach. You will not only learn how to exploit an application using different kind of injection attacks, but also develop the vulnerable applications from scratch in which you will have a common web login module with Thymeleaf and Bootstrap for a basic front-end, with Spring security form login authentication & authorisation, and with separate applications for SQL, NoSQL and LDAP injections. The applications will be developed using Java, Spring boot and Spring Data along with the most used data sources, such as PostgreSQL for SQL Injection, MongoDB for NoSQL injection and OpenLDAP for LDAP injection. In each section there will be;Development of the vulnerable web application using Java, Spring boot and Spring securityHacking of the application with various attack payloads and with Ethical hacking examplesProtection steps and the implementations to prevent injection attacksAt the end of the course you will understand the different type of injection vulnerabilities, perform injection attacks against the vulnerable web applications you have developed, and learn how to protect your applications against the injection attacks using various techniques such as,Validation and sanitisation using white list approachParametrised queries with prepared statementsEscaping outputUsing secure trusted librariesError handling and loggingGeneral coding practicesIf you want to skip the development and only perform the hacking of applications, you can jump into the injection lectures and download the source code provided in the resources section of that lecture. The source codes are in lecture 20 (SQL Injection), lecture 38 (NoSQL Injection), lecture 51 ( LDAP Injection), lecture 60 (LOG Injection) and lecture 74 (CSV Injection). Be aware that you will still need to install PostgreSQL for SQL Injection, MongoDB for NoSQL injection and OpenLDAP docker container for LDAP injection. You can see how to install and configure these data sources in the beginning lectures of each injection section. Manoj Singh: "Talented instructor and great course!!! Just a small suggestion, If you could add a chapter about "Broken Access Control" topic that will be a great help."For more detailed information on the progress of this course, you can check the introductory video and free lessons, and if you decide to enroll in this course, you are always welcome to ask and discuss the concepts and implementation details on Q/A and messages sections. I will guide you from start to finish to help you successfully complete the course and gain as much knowledge and experience as possible from this course.Remember! There is a 30-day full money-back guarantee for this course! So you can safely press the 'Buy this course' button with zero risk and join this learning journey with me.
Who this course is for:
Developers keen on web security, ethical hacking and secure coding,One wants to dive into injection vulnerability with different attack types,One likes to learn with a hands-on approach