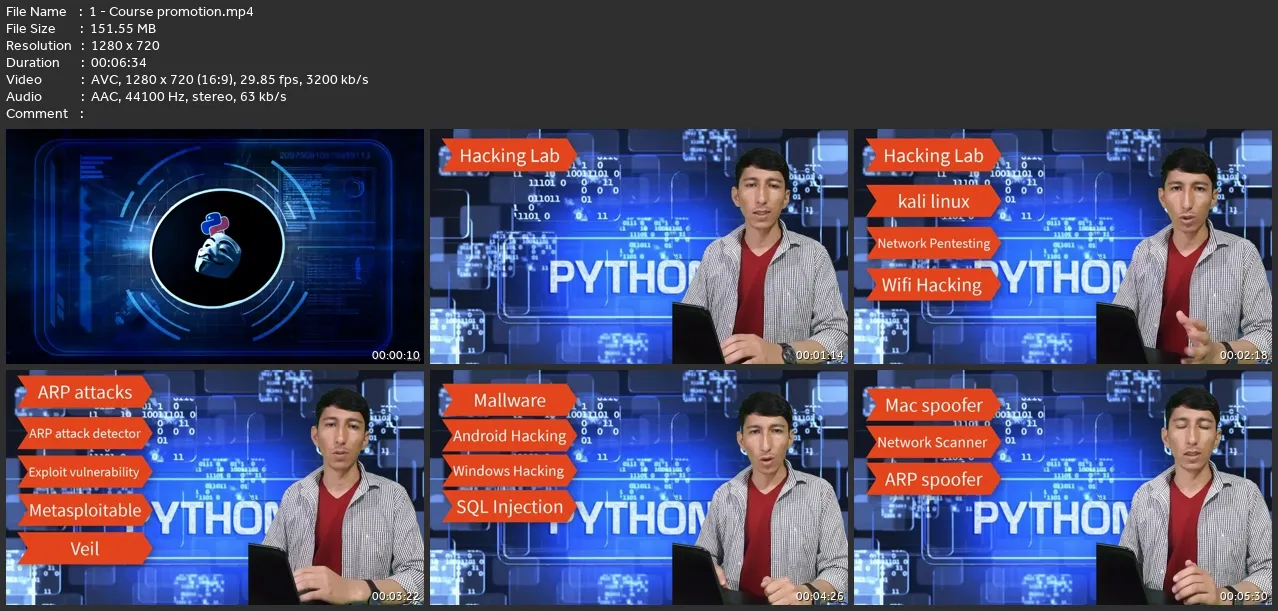
Python And Ethical Hacking: A Complete Cybersecurity Course
Last updated 2/2024
MP4 | Video: h264, 1280x720 | Audio: AAC, 44.1 KHz
Language: English (US) | Size: 7.43 GB | Duration: 22h 30m
Last updated 2/2024
MP4 | Video: h264, 1280x720 | Audio: AAC, 44.1 KHz
Language: English (US) | Size: 7.43 GB | Duration: 22h 30m
Become an Ethical Hacker and Learn: Network Security, Pentesting, python tools, Exploit | No prior knowledge required
What you'll learn
Introduction to Ethical Hacking
Understand the foundations, ethics, and legal aspects of ethical hacking.
Hacking Lab Setup.: Set up your own secure hacking laboratory using virtualization technologies like VirtualBox.
Install Windows and Kali Linux virtual machines while creating snapshots for easy system restore.
Kali Linux Basics:: Explore the essentials of Kali Linux, including basic commands and password management.
Network Pentesting:
Network Pentesting: Gain insights into network architecture and MAC addresses.
Deploy various wireless modes and explore network penetration testing.
Gathering Information from Networks: Learn packet sniffing techniques and employ tools like Airodump-ng for targeted packet sniffing.
Wireless Attacks: Master wireless attack strategies, such as fake authentication and WPA&WPA2 cracking.
Post Connection Attack: Utilize tools like Netdiscover, Zenmap, and Wireshark for post-connection attacks.
Explore hacking techniques on Windows and Android platforms.
Detection and Security: Detect ARP poisoning and suspicious activities using Wireshark.
Leverage Netdiscover with Netstalker for enhanced network security.
Gaining Access: Discover vulnerabilities in systems and exploit them using various techniques.
Attacks on Users: Create and test backdoors using Veil.
Achieve full control over Windows 10 and Android devices.
Beef
An introduction to the Browser Exploitation Framework (BeEF) and its capabilities.
Learn how to hook targets and extract passwords from different platforms.
Post Exploitation: Develop trojans with customizable icons, download/upload files, and capture keylogs.
Establish sustainable sessions within compromised systems.
Ethical Hacking Blueprint: Understand the ethical hacking blueprint and its importance in planning assessments.
Information Gathering: Utilize Netcraft and web crawlers for extensive information gathering.
Website Pentesting: Explore vulnerabilities such as code execution, file inclusion, and remote file inclusion.
MySQL: Familiarize yourself with MySQL and practice fundamental commands for data manipulation.
SQL Injection: Discover and exploit SQL injection vulnerabilities in both GET and POST methods.
Leverage tools like SQLMap for advanced exploitation.
Python Basics: Grasp the fundamentals of Python programming language required for hacking tasks.
Changing MAC Address with Python
Learn how to change MAC addresses programmatically using Python.
Mac Changer Algorithm Design: Understand the algorithm design for a MAC address changer using Python.
Network Scanner with Python: Build a network scanner tool using Python for scanning and enumerating network devices.
Writing an ARP Spoofer with Python: Create an ARP spoofer using Python to intercept network traffic.
Writing a Packet Sniffer with Python: Develop a packet sniffer using Python to capture and analyze network packets.
Writing a Packet Sniffer Detector with Python: Learn to build a packet sniffer detector using Python to detect suspicious network activities.
Writing Malware: Keylogger with Python
Build a keylogger malware using Python to capture keystrokes on a target system.
Backdoors: Explore techniques for creating backdoor malware for unauthorized access to systems.
Packaging with Python: Understand how to package Python programs into standalone executables for distribution.
Website Hacking with Python: Leverage Python for web application hacking and exploit various vulnerabilities.
Guess Login Password with Python: Develop a script in Python to perform brute-force attacks for guessing login passwords.
Writing a Vulnerability Scanner with Python: Create a vulnerability scanner using Python to identify and assess system vulnerabilities.
Requirements
Basic IT skills.
No Linux, programming or hacking knowledge required.
Computer with Minimum of 8GB ram/memory.
Operating system: Windows/Mac OS/ Linux
Description
Full Ethical Hacking Course: Unlock Your Cybersecurity Potential! Are you fascinated by the world of cybersecurity? Do you want to uncover vulnerabilities, protect systems, and make a difference in the digital landscape? Look no further than our comprehensive Full Ethical Hacking Course, designed to equip you with the skills and knowledge to thrive as an ethical hacker. Before you embark on this exciting learning journey, we provide a complete introduction to ethical hacking. Familiarize yourself with the principles, concepts, and importance of ethical hacking in today's increasingly connected world. Setting up your Hacking Lab is the first step, and our step-by-step instructions ensure you can effortlessly install VirtualBox in both Windows and Linux. Dive into the lab setup, including installing Windows and Kali Linux, along with essential tools like Metasploit. Learn to create snapshots for seamless experimentation and progress tracking. Mastering Kali Linux Basics is crucial for any ethical hacker. Gain a comprehensive overview while exploring fundamental commands and techniques. Ensure the security of your own Kali environment by learning how to change passwords effectively. Next, immerse yourself in the intricate world of Network Pentesting. Understand network fundamentals, decipher MAC addresses, and delve into wireless modes. Grasp the art of gathering valuable information from networks through packet sniffing and exploring Wi-Fi bands. Discover targeted packet sniffing techniques employing Airodump-ng. The wireless attack section empowers you to conduct fake authentications and crack WPA and WPA2 networks confidently. Explore the world of post-connection attacks using powerful tools such as netdiscover, zenmap, man-in-the-middle techniques, bettercap, and Wireshark. Unleash your prowess in hacking Windows and Android systems. Maintaining your edge in Detection and Security is paramount. Learn to detect and counter ARP poisoning attacks while unearthing suspicious activities using Wireshark. Leverage the combined powers of netdiscover and netstalker to fortify network security. Gaining Access is a key milestone in ethical hacking. Discover vulnerabilities within systems and exploit them effectively. Progress through a series of exploits, targeting different vulnerabilities methodically. Attacks on Users take your skills to the next level. Delve into the world of Veil and create your first backdoor. Test and achieve full control over Windows 10 and Android systems to understand the potential risks and devise mitigation strategies. Beef up your knowledge with an in-depth exploration of the Beef framework. Master the art of hooking targets, leveraging tools like Bettercap alongside Beef, and discovering email and Facebook passwords. Unleash the power of backdoor delivery mechanisms. Post-exploitation activities are essential in maintaining control and access. Develop trojans with customized icons, master file manipulation within target computers, capture keylogs stealthily, and ensure session sustainability. Understand the Ethical Hacking Blueprint, a framework that encapsulates the core concepts and methodologies of ethical hacking, providing a blueprint for structured and effective hacking. Information Gathering becomes a breeze with advanced techniques using Netcraft and crawlers. Enhance your website pentesting skills by exploiting basic vulnerabilities, achieving code execution, gaining full control of servers, and identifying file inclusion vulnerabilities. Immerse yourself in MySQL and its practical applications. Master essential operations like insertion, deletion, updating, and conditional selections. Harness the power of logical operators and sorting techniques. Unlock the secrets of SQL Injection and learn to identify and exploit vulnerabilities in both GET and POST methods. Discover sensitive information within databases and leverage the powerful SQLMap tool for automated injection. Python Basics form the foundation for your hacking journey, enhancing your capabilities with versatile scripting. Learn to change MAC addresses using Python, design efficient MAC changer algorithms, and build network scanners, ARP spoofers, packet sniffers, and detectors with Python. Take your skills to the next level by understanding the process of malware creation. Uncover the secrets of developing keyloggers, backdoors, and explore packaging techniques for effective deployment. Harness the power of Python in Website Hacking and strengthen your ability to guess login passwords effectively. Develop a powerful vulnerability scanner, empowering you to identify weaknesses and secure systems proactively. By the end of this course, you'll possess comprehensive knowledge of ethical hacking, from lab setup and network pentesting to website exploitation, Python scripting, and vulnerability scanning. Gain practical skills through hands-on exercises and real-world examples, preparing you for a successful career in cybersecurity. Enroll now and embark on your journey to becoming an ethical hacking expert. Join a community of passionate learners and set yourself apart in the world of cybersecurity! #EthicalHacking #Python #Cybersecurity
Who this course is for:
Anybody Interested in Learning Ethical Hacking / Penetration Testing.,Anybody interested in learning how hackers hack computer systems.,Any body interested in learning how to secure systems from hackers