Ethical hacking with python and kali Linux from scratch
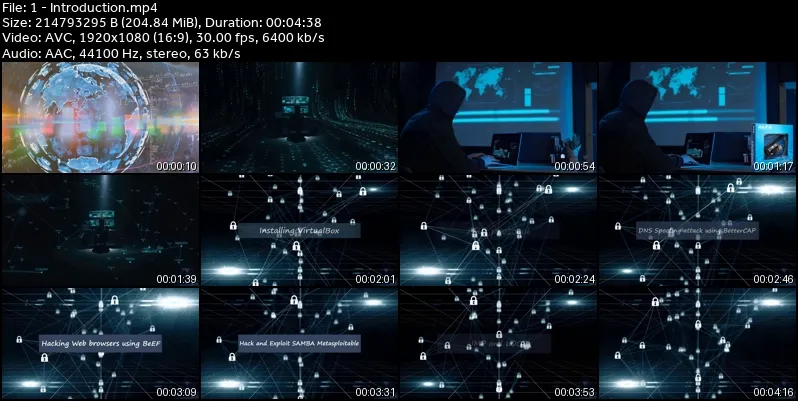
MP4 | Video: h264, 1920x1080 | Audio: AAC, 44.1 KHz
Language: English (US) | Size: 10.67 GB | Duration: 12h 26m
MP4 | Video: h264, 1920x1080 | Audio: AAC, 44.1 KHz
Language: English (US) | Size: 10.67 GB | Duration: 12h 26m
Learn how to become an Ethical Hacker using Python and Kali Linux to perform penetration testing on networks.
What you'll learn
Installation of Virtual Box & Kali Linux.
Learn ethical hacking and cyber security, python programming and kali linux scripting at the same time
Install hacking lab on Windows 10 operating system
Know what is hacking and cyber security
Install windows 11 on virtualBox
Install virtualBox on windows
Install kali Linux on virtualBox
Use kali Linux terminal
Understand different network layers such as ARP, HTTP
Use Wireshark to see how TCP protocol uses a three-way handshake to establish a network connection, such as http protocol
Use Wireshark to see how UDP protocol is used in a network such as DHCP protocol
Use Wireshark to see how ICMP protocol is used for testing connectivity, such as ping tool
Use Wireshark to see how ARP protocol is used in internal networks to map IPv4 addresses to MAC addresses
Learn the difference between IPv4 and IPv6 ,private and public IP addresses, Subnets and CIDR, port numbers.
Learn how to use NetDiscover to scan a network ,using active or passive scanning, and how to scan multiple networks
Use Nmap tool to scan a port or a range of ports
Use Nmap for TCP port scan ,without fully connecting to the target device
Use Nmap for UDP port scan, and how to use timing options
Use Zenmap which is a GUI version of Nmap
Downgrade HTTPS to HTTP
Intercept and modify network packets
Create a Hidden Bind TCP payload using Msfvenom
Create a reverse TCP payload using Msfvenom
Creating backdoors using TheFatRat
Hide payloads behind images
Hack a Web Browsers using BeEF
Evade Antivirus with Veil-Evasion
ARP poisoning with Arpspoof
Installing Metasploitable 2 in VirtualBox
Using Hydra password cracking tool
Know how to launch JavaScript Injection attack
Exploit port 21 FTP Server
Hack and Exploit port 22 SSH Metasploitable 2
Hack and Exploit Port 23 Telnet Metasploitable 2
Hack and Exploit Ports 512-513-514 netkit-rsh Metasploitable 2
Hack and Exploit SAMBA Metasploitable 2
Learn how to Connect to WiFi wireless network
Install Wireless adapter
Create Ad Hoc WiFi
Learn how to attack a computer using Denial of Service Attack using MKD3
Use Fern WiFi Cracker to crack a password
Hack wireless network using Airgeddon
Uncover hidden SSID
Create password wordlist using crunch and save the output in a file
Use aircrack-ng to test the keys in the worldlist
Use filter in wireshark
Use aireplay to launch deauthentication attack
Run dictionary attacks to guess username and password
Use airodump to sniff and capture packets and to see all wireless in the area
Analyze the wireless networks
Learn the basics of assembly language
Know what are the reserved words and identifiers such as MOV , SUB,NOP in assembly language
Know what are Boolean and comparison instruction such as AND,XOR,CMP in assembly language
Learn how to convert Pseudocode to assembly language
Know what are Mnemonic, operands and labels in assembly language
Know how to declare a variable if it is byte, word or double word or signed variable in assembly language
Know how to use jump based on sign or flag and loop, and the difference between local and global labels
Use while loop in assembly language
Know what are Little Endian and big-Endian order in assembly
Know when overflow occurs
Know how Stack operations work ,and how to use procedures
Use PUSH, POP and LEA instructions in assembly language
Know how to CALL a PROCEDURE in assembly language
Know types of registers and what are they used for in assembly language
Install Immunity Debugger on Windows 10 machine
Use Immunity Debugger
Install Visual Studio Code and Mingw 64 on Windows 10
Stack Overflow Exploitation using VulnServer
SyncBreeze 10.0.28 Buffer Overflow attack
Install VulnServer on Windows 10
Write a python program to test the crash of a target machine using TRUN
Use sockets to send data over TCP
Use pattern creation to launch an attack
Use python scripting to find offset location of EIP register in the target machine
Use python scripting to control EIP register in the Vulnserver target machine
Use python scripting to send payload to Vulnserver target machine
Install SyncBreeze 10.0.28 on windows 10 machine
Instal python 2.7 on windows 10 machine
Install mona on Windows 10 machine
Hack a remote machine by manipulating a username using a long string to crash the application and lead to memory corruption
Use python scripting to build a fuzzer
Use python scripting to test the connectivity with the server
Use python scripting to send multiple HTTP post requests with long usernames
Use python scripting to generate all possible hexadecimal numbers from 00 to FF
Use python scripting to find bad characters
Use python scripting to create a shell code payload without bad characters
Use Mona to search for the hexadecimal of an opcode in dll file
Requirements
Computer device with a minimum of 4GB memory, and Windows, OS X or Linux operating System.
Wireless adapter with packet sniffing capabilities (for the wireless attacks section)
No hacking knowledge required.
Description
Ethical hacking is used to ensure that any network is secure. This course will provide information about different software and tools that you can use when you are performing an ethical hack. There are some sample programs in the course that you can use to begin the ethical hacking process.This course has different tools that you can use to test the network for any vulnerabilities. Once you identify the vulnerabilities, you can work towards improving network security. If you do not know how a hacker thinks, you may not be able to test the system well. This course for you ,if you want to learn more about how to test the vulnerabilities in a system or network and want to fix those vulnerabilities.This course will cover the following topics:Setting up a penetration test environment to practice hacking safely:Installing VirtualBox on Windows 10.Installing Kali Linux on VirtualBox.Installing Windows 11 on VirtualBox.Installing Visual Studio Code on Kali Linux.Installing Metasploitable 2 in VirtualBox.Installing Immunity Debugger on Windows 10.Installing Visual Studio Code and Mingw 64 on Windows 10.Installing mona on Windows 10.Connecting to WiFi wireless network.Installing Wireless adapter.Hacking topics:Network basics, all you need to know about ARP protocol, TCP protocol, UDP protocol, ICMP protocol and IP addressing.Information gathering using different tools such as Netdiscover, Nmap and Zenmap.Man in the middle attacks which includes ARP poisoning using BetterCAP and EtterCAP, DNS spoofing attacks using BetterCAP and EtterCAP.Client side attacks, such as creating a reverse TCP or a hidden bind TCP using Msfvenom, hide payloads behind images, ARP poisoning with Arpspoof, creating backdoors using TheFatRat, Evading Web browsers using BeEF .Server side attacks, such as Hack and exploit ports 21 FTP, 22 SSH , 23 Telnet Metasploitable 2,Hack and exploit ports 512,513,514 netkit-rsh Metasploitable 2,Hack SAMBA Metasploitable 2,Using Hydra password cracking tool.Exploit the stack using the buffer overflow, Stack overflow exploitation using VulnServer, and SyncBreeze 10 0 28 Buffer Overflow attack.Wireless attacks, such as hacking passwords using Dictionary Attack and Brute Force Attack, uncover hidden SSID, Hack wireless network using Airgeddon, luanch Denial of service attack using MKD3,Hacking passwords using Fern WiFi Cracker, creating Ad Hoc WiFi.Programming topics:Assembly languagewhere you will learn Types of registers.Data transfer instructions.Little Endian and big Endian order.Defining data.Boolean and comparison instructions.Conditional structure.Jump and loop instructions.Stack operations and using procedures .And overflow.Python programmingImplement the following hacking programs using python scripting:Find offset location of EIP register in the target machine.Control EIP register in the Vulnserver target machine.Send payload to vulnserver target machine.Build a fuzzer.Test the connectivity with the server.Send multiple HTTP post requests with long usernames.Generate all possible hexadecimal numbers from 00 to FF.Find bad characters.Create a shell code payload without bad characters.Notes:Please note the information contained in this course is for educational purposes only
Who this course is for:
Anyone who wishes to become an Ethical Hacker or Penetration Tester in the field of Information Security., Anyone who wishes to learn python programming, Anyone who wishes to learn Linux scripting